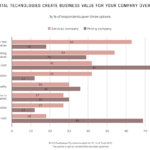
“Cybersecurity needs to be approached through a strategic risk management process with the identification and prioritisation of known threats and vulnerabilities.” Perhaps surprisingly, the … read more …
Cybersecurity: Governance & strategic risk management
Business models: Rapid rate of change
Mining industry business models have been relatively stable over the last two decades, through a period in which most other industries have undergone significant … read more …
Media Release: ELECTRICS TO DRIVE ZERO EMISSION MINES
Heightened social pressure and a need for economically efficient mining practices will see Australia’s mining industry shift towards a future of automation, electrification and … read more …
Geopolitics: an inevitable chaos
It’s all a game Resource security is a global geopolitical game that has been played for centuries. Some play to primarily make money through … read more …
Forecasters or fortune tellers?
Improvements in data, analytics and decision-support systems have improved our ability to forecast the future. Some of the hype may be unfounded but within … read more …
Mining’s methane problem
All of mining’s recent investments in renewable energy and electrification will count for little if it does not confront its methane problem. Over a … read more …
Cybersecurity: A catastrophic catalyst
Historically, resources industries have been shaped by catastrophic events which jolt the industry out of inertia and into action. Could the same be the … read more …
Introducing the State of Play: Strategy serialised report
Strategy design is dynamic process. It requires an innate understanding of the external environment, as well as a clear-eyed view of internal capability to … read more …
State of Play: Ecosystem – Low footprint mining innovation
As the scale and ambition of mining projects has increased, so too has the environmental footprint they have left behind. However, a range of … read more …
State of Play: Cybersecurity – Shift to modern digital architectures
“Most mining companies have legacy infrastructure in place that both poses high security risk as well as being an impediment to the adoption of … read more …